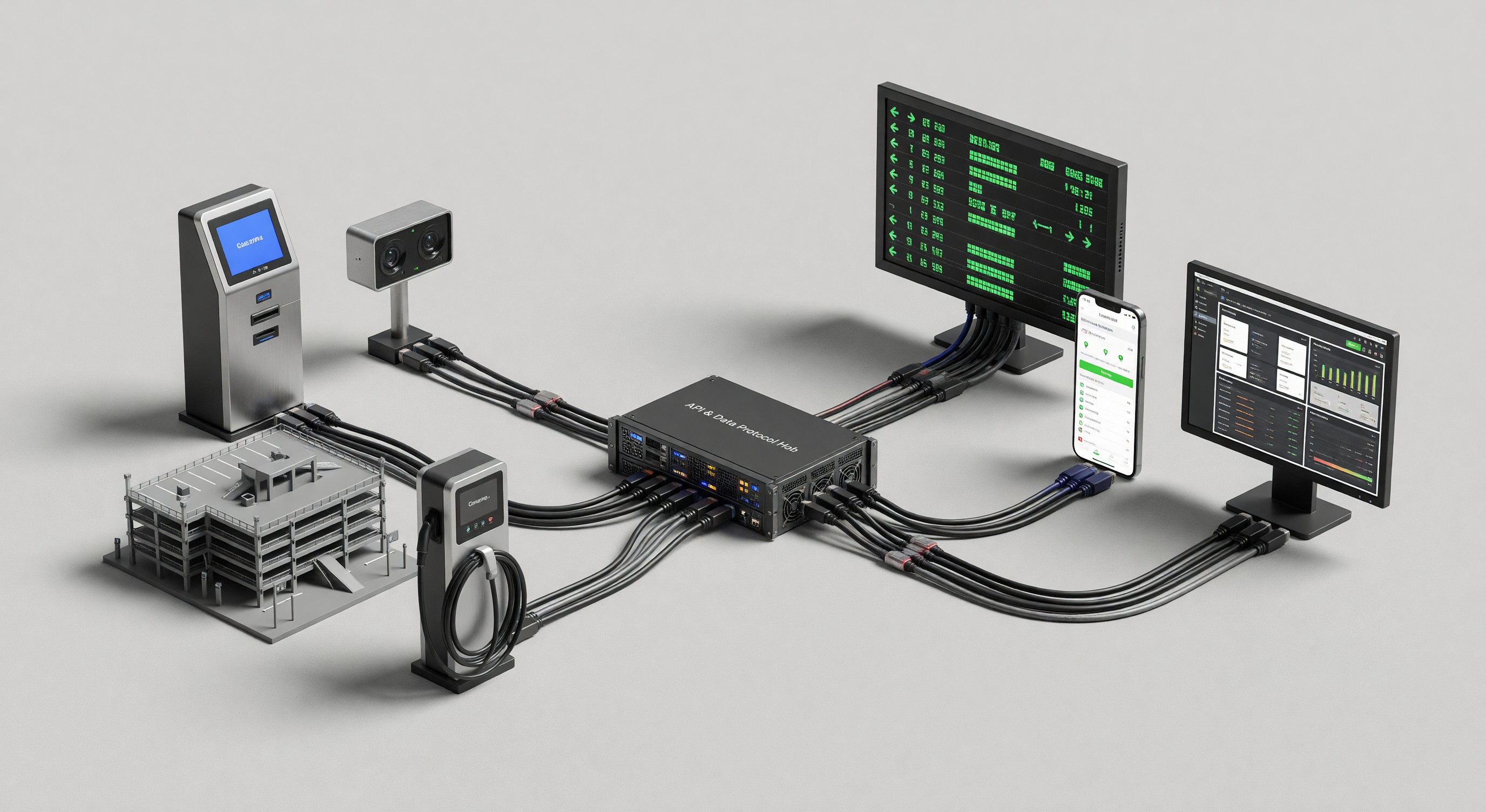
Parking facilities operate networked technology infrastructure — PARCS, LPR cameras, payment terminals, access control systems, CCTV, and increasingly EV charging equipment — that is connected to the internet and therefore exposed to cybersecurity risks that did not exist in earlier generations of standalone parking equipment. A payment terminal breach, a ransomware attack on the PARCS management server, or unauthorized access to the access control system can disrupt operations, compromise customer data, and create legal and financial liability. Cybersecurity in parking is no longer optional — it is an operational requirement for facilities with connected technology.
Cybersecurity Threats to Parking Facilities
Payment card data theft: Payment terminals and PARCS systems that handle card data are targets for malware designed to capture card data during transactions. Point-of-interaction (POI) device attacks — injecting malware into pay station software to capture card data at the moment of card swipe — have affected multiple retail industries including parking.
Ransomware: Ransomware attacks encrypt the victim’s data and demand payment for the decryption key. A ransomware attack on the PARCS management system can disable access control, payment processing, and operational reporting — effectively shutting down the facility. Ransomware attacks on parking operators have occurred; the PARCS vendor’s network connectivity between facilities creates a potential propagation path.
Unauthorized access to access control systems: The access control system determines which vehicles can enter a facility. Unauthorized modification of the access control database — adding permit records, deactivating legitimate accounts, or disabling gate control — can result in unauthorized access or legitimate customer denial. Access control systems connected to the internet require strong authentication and logging.
LPR data exfiltration: LPR systems accumulate extensive vehicle movement data. Unauthorized access to LPR databases can expose the location history of thousands of individuals — creating privacy liability and potential misuse of movement data.
CCTV compromise: Security camera systems connected to the internet are frequent targets for unauthorized access. Compromised cameras may be disabled (defeating their security purpose), used to surveil private areas, or enlisted in botnets.
EV charging infrastructure attacks: EV charging equipment connected to charging management networks has been demonstrated to be vulnerable to remote manipulation — including firmware modification and service denial. OCPP-connected chargers require the same network security attention as other internet-connected facility equipment.
Network Security for Parking Facilities
Network segmentation: Parking technology equipment should be segmented on its own network (VLAN) separated from office networks, guest WiFi, and tenant networks. A compromised pay station on a shared network can be used as a pivot point to access administrative systems; a segmented pay station network limits the blast radius of a compromise.
Firewall rules: Parking equipment networks should have firewall rules that permit only the specific communication required for operations — pay stations communicating with the payment processor, PARCS controllers communicating with the management server — and block all other traffic. Default-deny firewall rules (block everything not explicitly permitted) are more secure than default-allow rules.
Firmware management: IoT parking equipment (cameras, pay stations, gate controllers) runs firmware that may contain security vulnerabilities. Vendors release firmware updates to patch vulnerabilities; operators who do not apply updates allow known vulnerabilities to persist. Establish a firmware update policy that applies vendor-released security updates within a defined period (30 to 60 days for critical patches).
Remote access security: Remote access to PARCS management systems (for vendor support and operator administration) should use VPN or zero-trust network access methods rather than direct internet-facing RDP or SSH. Vendor remote access should be limited to defined time windows and logged.
PCI DSS Compliance
Any parking facility that accepts credit or debit card payments is subject to Payment Card Industry Data Security Standard (PCI DSS) requirements. PCI DSS specifies security requirements for systems that process, store, or transmit cardholder data:
Scope reduction: The primary PCI DSS strategy for most parking operators is scope reduction — using certified payment terminals that handle card data entirely within the terminal hardware, never transmitting raw card numbers to PARCS servers or the operator’s network. Point-to-point encryption (P2PE) and tokenization solutions, when properly implemented, significantly reduce PCI scope.
Self-assessment questionnaire (SAQ): Most parking operators qualify for a reduced scope SAQ (SAQ P2PE for operators using certified P2PE solutions) rather than a full PCI DSS assessment. The specific SAQ type depends on how card data is handled.
Annual compliance validation: PCI DSS requires annual validation — completion of the appropriate SAQ or, for larger operations, a qualified security assessor (QSA) assessment. Non-compliance does not eliminate the card network’s ability to hold the operator liable for card fraud losses.
Vendor PCI compliance: Payment terminal vendors, payment processors, and PARCS vendors who handle card data must maintain their own PCI compliance certifications. Operators should confirm PCI compliance status of all technology vendors involved in payment processing.
Access Control Security
Multi-factor authentication (MFA): PARCS management systems, access control administration portals, and cloud platforms should require MFA for all administrative accounts. Password-only authentication is inadequate for systems controlling physical access.
Principle of least privilege: User accounts in PARCS and access control systems should have only the permissions necessary for their role. A cashier account should not have access to rate configuration or permit management. An enforcement officer account should have read access to permit records but not modification rights.
Administrative account audit: Periodically review all administrative accounts in PARCS and access control systems. Deactivate accounts for former employees, vendor personnel whose engagement has ended, and any accounts whose purpose is unclear.
Audit logging: All administrative actions in PARCS and access control systems should be logged with the user identity, timestamp, and action taken. Audit logs should be retained for a period sufficient to support incident investigation (minimum 12 months).
Incident Response Planning
Parking facilities should have documented incident response procedures for cybersecurity events:
Ransomware response: If PARCS systems are encrypted by ransomware, the immediate priorities are: isolate affected systems from the network (to prevent propagation), notify the PARCS vendor for emergency support, assess operational impact, and determine whether manual fallback operations are possible while systems are restored. A tested backup and restoration procedure reduces the leverage ransomware has — operators who can restore from a clean backup within hours have far less pressure to pay ransom than those with no restoration path.
Payment card breach response: If a payment card breach is suspected, the immediate actions include: notify the payment processor and acquiring bank, preserve evidence (do not wipe compromised systems), engage a PCI Forensic Investigator (PFI) if required by the card networks, and assess notification obligations under applicable state data breach laws.
Contact list: Incident response procedures should include an up-to-date contact list: PARCS vendor emergency support, payment processor security team, cybersecurity incident response service (if retained), legal counsel, and management chain escalation.
Vendor Security Evaluation
Security questionnaire: When evaluating PARCS, payment, LPR, or access control vendors, include a security questionnaire that addresses: SOC 2 Type II audit status, PCI compliance certifications, vulnerability disclosure and patch cadence, penetration testing frequency, and data breach notification commitments.
Cloud platform security: Cloud-based parking platforms must demonstrate security controls appropriate for platforms that store customer payment data and access credentials. Request evidence of encryption (at rest and in transit), access control architecture, and security monitoring practices.
Contract security provisions: Parking technology contracts should include: data breach notification obligation (within a defined period of vendor awareness), security incident cooperation obligations, and right to audit security controls.
Frequently Asked Questions
Is parking facility cybersecurity a significant risk? Yes. Parking facilities operate payment infrastructure, access control, and surveillance systems that are attractive targets for cybercriminals. Payment card data theft and ransomware are the highest-probability threats. The consequences — regulatory fines, card brand liability, operational disruption, and reputational damage — are material. The appropriate response is risk management, not dismissal.
What is the minimum cybersecurity posture for a parking facility? At minimum: network segmentation for parking equipment, MFA for all administrative accounts, current firmware on all equipment, PCI DSS compliance validation, and a tested backup and restoration procedure for PARCS management systems.
How often should parking facilities conduct security assessments? Annual third-party security assessments are appropriate for larger facilities with significant payment volume or large monthly parker databases. Smaller facilities can maintain security posture through annual internal assessment against a defined checklist (firmware updates, account audits, firewall rule review) supplemented by vendor security assurance.
What should a parking operator do if they suspect a payment card breach? Immediately notify the payment processor and acquiring bank. Follow the incident response procedures established in the payment acceptance agreement. Do not attempt to investigate the breach by modifying or wiping potentially compromised systems — evidence preservation is required. Engage legal counsel early; data breach notification laws apply in most states.
Takeaway
Cybersecurity for parking facilities is a legitimate operational requirement, not an esoteric IT concern. Payment terminals, PARCS management systems, LPR cameras, and access control systems are all potential attack surfaces for threats that can disrupt operations, compromise customer data, and create regulatory liability. The baseline security posture — network segmentation, MFA, firmware management, PCI compliance, and incident response planning — is accessible for facilities of any size and should be incorporated into parking technology management alongside equipment maintenance and software updates. The cost of baseline security is far lower than the cost of responding to a breach.
Further Reading from Authoritative Sources
- NIST Cybersecurity Framework for parking and transportation infrastructure — NIST publishes the Cybersecurity Framework, payment security standards, and IoT security guidelines that directly inform the network security, access control, and incident response practices described in this article.
- DOE EV charging infrastructure cybersecurity research and OCPP security guidance — The U.S.